N7x
1 week ago
•
100%
N7x
1 week ago
•
100%
Thanks!
Found this interesting list: https://list.latio.tech/ On the open source side, there is https://www.dependencytrack.org/
 N7x
1 month ago
•
100%
N7x
1 month ago
•
100%
Oh nice, wasn't aware of this, definitely looks interesting, thanks! I am an OSCP holder as well.
 www.offsec.com
www.offsec.com
 www.offsec.com
www.offsec.com
cross-posted from: https://infosec.pub/post/8123190 > Hello everyone, > > > I work in appsec, my manager would like to send us to a conference this year. We are based in Europe, and the company would like to across intercontinental travel. > > I have OWASP Global 2024 in Lisbon on my radar, as well as the BlackHat EU in London, is there any other conference you guys would recommend?
Hello everyone, I hope this post belongs here, otherwise I'll move it to [!appsec@infosec.pub](https://infosec.pub/c/appsec). I work in appsec, my manager would like to send us to a conference this year. We are based in Europe, and the company would like to across intercontinental travel. I have OWASP Global 2024 in Lisbon on my radar, as well as the BlackHat EU in London, is there any other conference you guys would recommend?
 N7x
8 months ago
•
100%
N7x
8 months ago
•
100%
Why the downvotes? This is a call for speakers to a security conference
 appsec.beehiiv.com
appsec.beehiiv.com
 N7x
8 months ago
•
100%
N7x
8 months ago
•
100%
Great!
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
Write-up: https://lock.cmpxchg8b.com/zenbleed.html
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
 thehackernews.com
thehackernews.com
 www.reuters.com
www.reuters.com
cross-posted from: https://lemmy.capebreton.social/post/82259 > OSLO, July 24 (Reuters) - Twelve Norwegian government ministries have been hit by a cyber attack, the Norwegian government said on Monday, the latest attack to hit the public sector of Europe's largest gas supplier and NATO's northernmost member. > > "We identified a weakness in the platform of one of our suppliers. That weakness has now been shut," Erik Hope, head of the government agency in charge of providing services to ministries, told a news conference. > > The attack was identified due to "unusual" traffic on the supplier's platform, Hope said, declining to provide specifics. It was uncovered on July 12 and was being investigated by police. > > "It is too early to say who is back this and what is the extent of the impact (of the attack)," he said.
 www.dignitymemorial.com
www.dignitymemorial.com
RIP
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
Thanks!
 www.bleepingcomputer.com
www.bleepingcomputer.com
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
Finally done with my 120 CPEs for my CISSP. That was a long ride, happy to be done with it
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
Thank you for this!
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
Be careful, 2FA still has issues at the moment: https://github.com/LemmyNet/lemmy/issues/3309
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
Same here
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
Impressive list!
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
They should be fixed Indeed
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
Thank you!
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
Interesting, I didn't even know it was him too
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
Oh yes sorry for that, should have posted the one you linked
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
Well, I guess there is a compromise to be found between aggregating content from different instances, and consuming a tremendous amount of resources on the server to do so.
As an example, it seems reasonable to me for someone to aggregate content from other security/IT instances here, but not let's say gardening or language learning.
And about the number of accounts, I have one for infosec, and a few others, each for every interest I have
 www.reversinglabs.com
www.reversinglabs.com
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
You have to search them first.
As a side comment, I'm not sure this instance should be federated with fitness communities, as it doesn't seem really related to the domain of infosec
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
I see you also like Absolute Appsec.
I just started a more specialized AppSec list here: https://infosec.pub/post/318834, can I link you comment there?
There is a nice list of Infosec podcasts here: https://infosec.pub/post/152754 What are your more specialized appsec recommendations?
 sec-consult.com
sec-consult.com
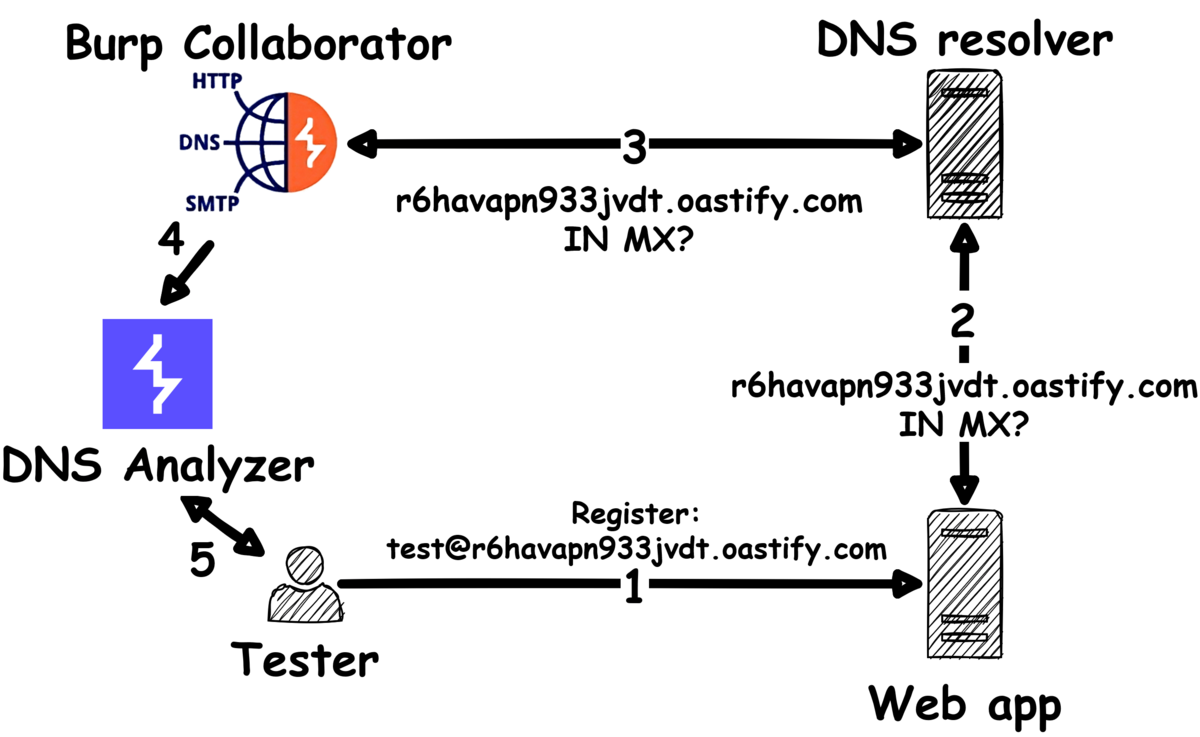
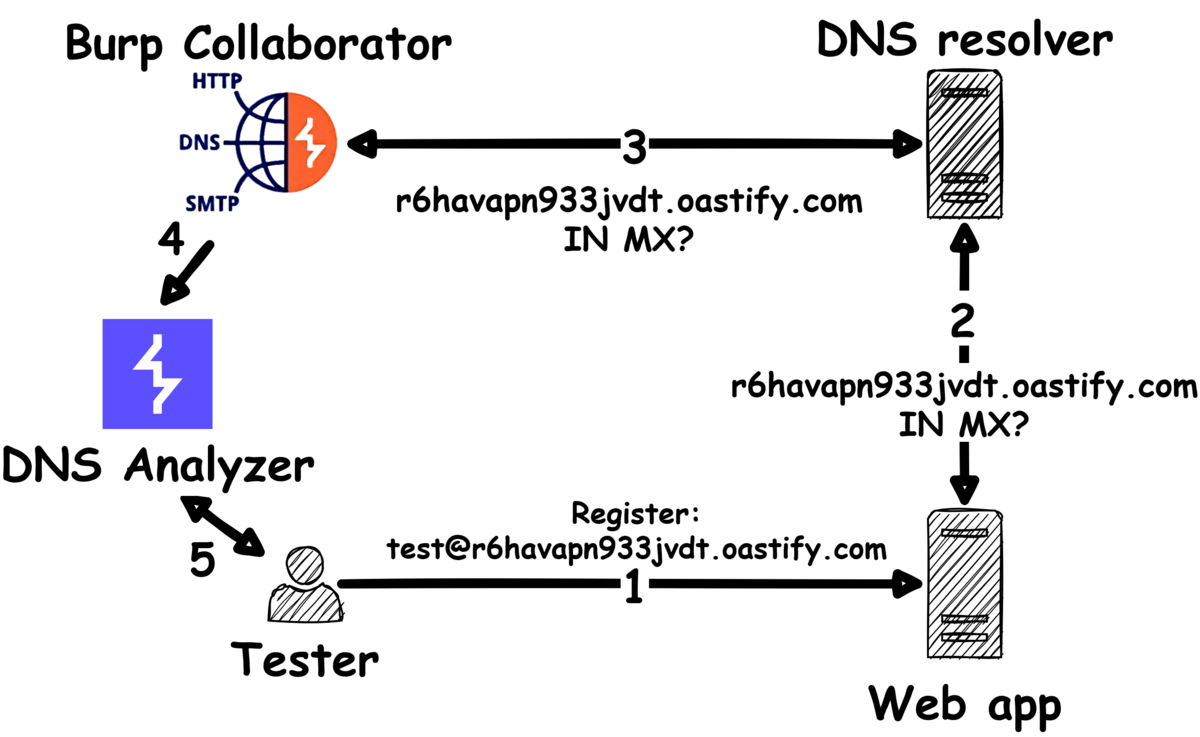
A brand-new Burp Suite extension for discovering DNS vulnerabilities in web applications.
 portswigger.net
portswigger.net
You might have found HTML injection, but unfortunately identified that the site is protected with CSP. All is not lost, it might be possible to bypass CSP using DOM clobbering, which you can now detect using DOM Invader! In this post we’ll show you how. We’ve based the test case on a bug bounty site, so you’re likely to encounter similar code in the wild. If you’re unfamiliar with DOM clobbering then head over to our Academy to learn about this attack class and solve the labs.
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
Nix has been on my radar for a while too. The approach is takes to reproducibility looks very interesting
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
I'm also going to post it as much as I can. I love the idea of having a lemmy instance dedicated to infosec, we just need a few more people on board.
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
Thank you!
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
Have a look at https://lemmy.world/post/465785
 portswigger.net
portswigger.net
You might have found HTML injection, but unfortunately identified that the site is protected with CSP. All is not lost, it might be possible to bypass CSP using DOM clobbering, which you can now detect using DOM Invader! In this post we'll show you how. We've based the test case on a bug bounty site, so you're likely to encounter similar code in the wild. If you're unfamiliar with DOM clobbering then head over to our Academy to learn about this attack class and solve the labs.
 sec-consult.com
sec-consult.com
A brand-new Burp Suite extension for discovering DNS vulnerabilities in web applications.
 sec-consult.com
sec-consult.com
 N7x
1 year ago
•
100%
N7x
1 year ago
•
100%
Hello Jerry, Just wanted to say Thank you for hosting this! Seems like a great opportunity for infosec professionals to discuss topics